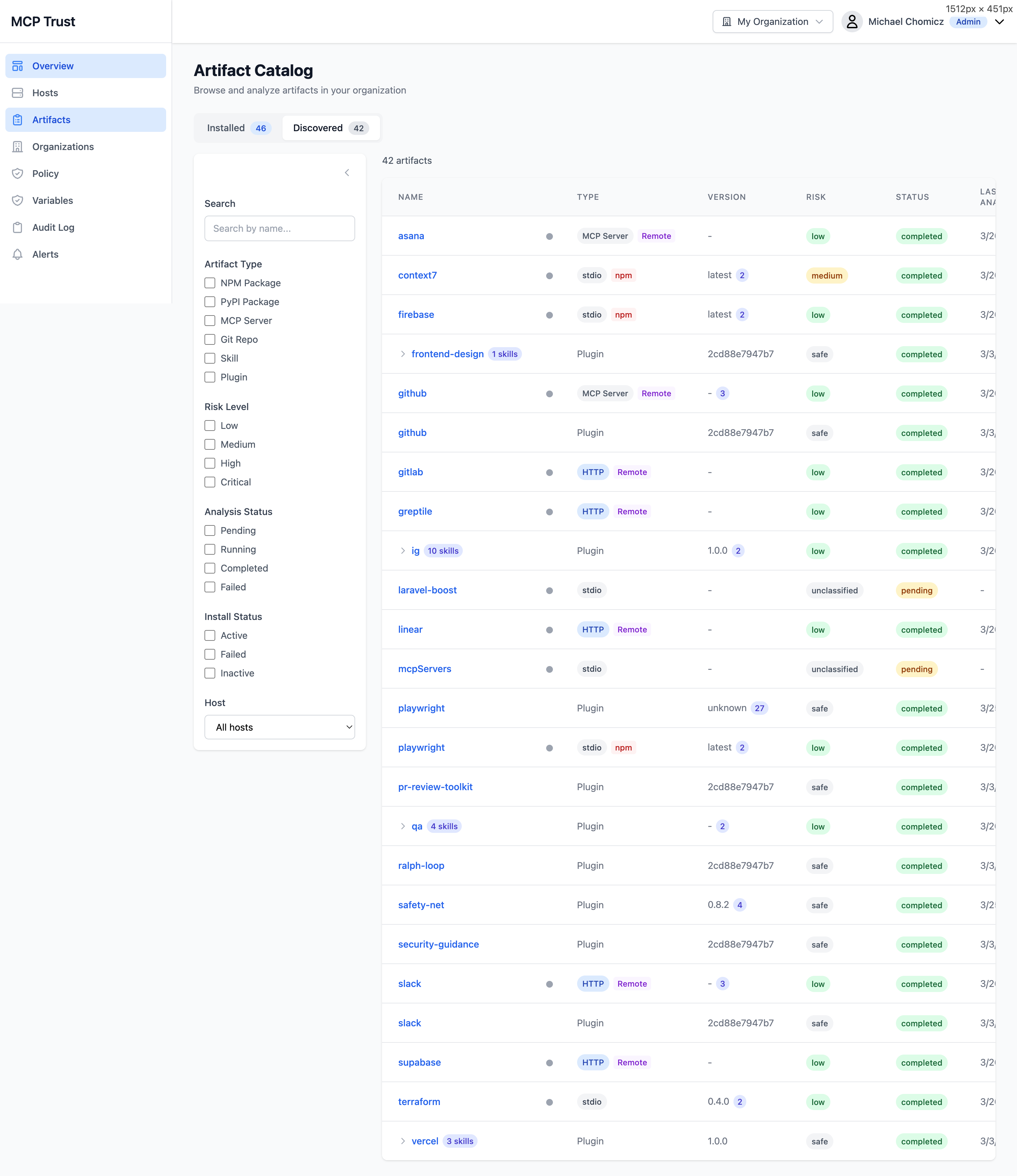
| Pre-Install Artifact Scanning |
|
Source Code Analysis (SAST)
Static analysis of MCP server and plugin source code
|
YesPython, shell, JS/TS |
No |
No |
No |
No |
|
Dependency Vulnerabilities (SCA)
Known CVEs in transitive dependencies
|
YesOSV + Trivy/Grype |
No |
No |
No |
No |
|
Secrets Detection
Hardcoded API keys, tokens, private keys in source
|
Yes25 rule types |
No |
No |
No |
No |
|
Container Image Scanning
Layer extraction, SBOM generation
|
Yes |
No |
No |
No |
No |
|
MCP Tool Schema Analysis
Tool poisoning, shadowing, overly broad schemas
|
Yes |
No |
PartialConfig-level |
No |
PartialHygiene checks |
|
Skill & Plugin Scanning
Prompt injection, data exfiltration, role hijacking
|
Yes37+ skill, 52+ hook rules |
No |
No |
No |
No |
| Install-Time Enforcement |
|
Plugin Install Interception
Quarantine, scan, and gate before plugins load
|
YesScan before load |
No |
No |
No |
No |
|
Risk Threshold Policy Gate
Org-configurable score thresholds with admin overrides
|
YesServer-side policy |
No |
No |
No |
No |
|
Admin Approval Workflow
Dashboard review of blocked plugins with approve/deny
|
YesSARIF + findings in dashboard |
No |
No |
No |
No |
|
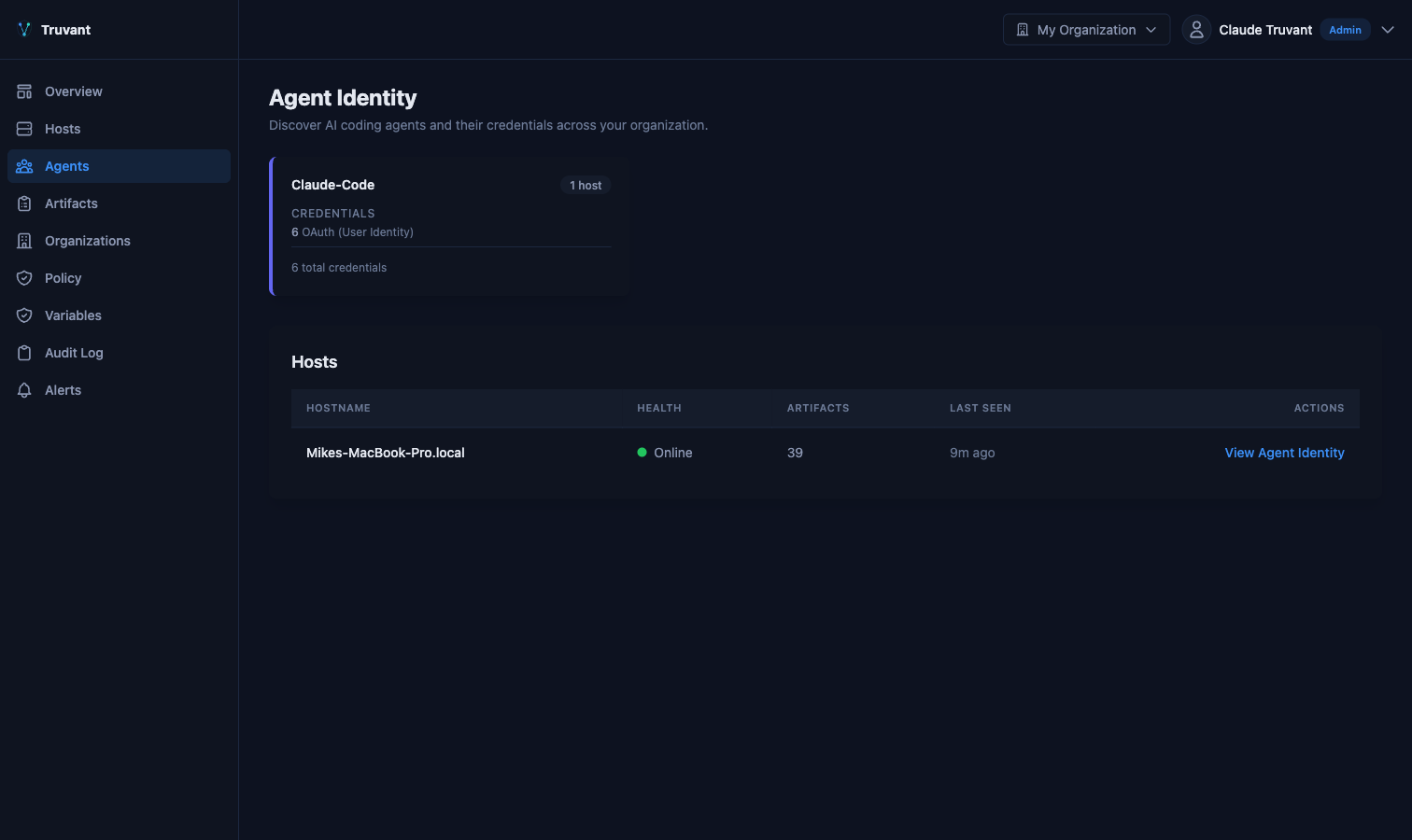
AI Tool Integration
Seamless enrollment into Claude Code, Cursor, Copilot
|
YesAutomatic enrollment |
No |
No |
No |
No |
| Runtime Enforcement |
|
System Command Interception
Block ssh, kubectl exec, git push --force from agents
|
YesSubcommand-level granularity |
No |
No |
No |
No |
|
AI Agent Caller Detection
Only enforce on AI agents — humans pass through unaffected
|
YesClaude, Cursor, Copilot |
No |
No |
No |
No |
|
MCP Tool-Call Policy (HTTP)
Per-tool allow/deny on remote MCP endpoints
|
YesPer-tool allow/deny |
PartialBehavioral monitoring |
YesAgent-level interception |
No |
YesMCP proxy server |
|
MCP Tool-Call Policy (Local Stdio)
Policy enforcement on local MCP servers (npx, uvx)
|
YesTransparent enforcement |
No |
PartialEndpoint agent |
No |
No |
|
Tamper Protection
Detects and alerts on bypass attempts
|
YesMandatory enforcement mode |
No |
No |
No |
No |
| Monitoring & Compliance |
|
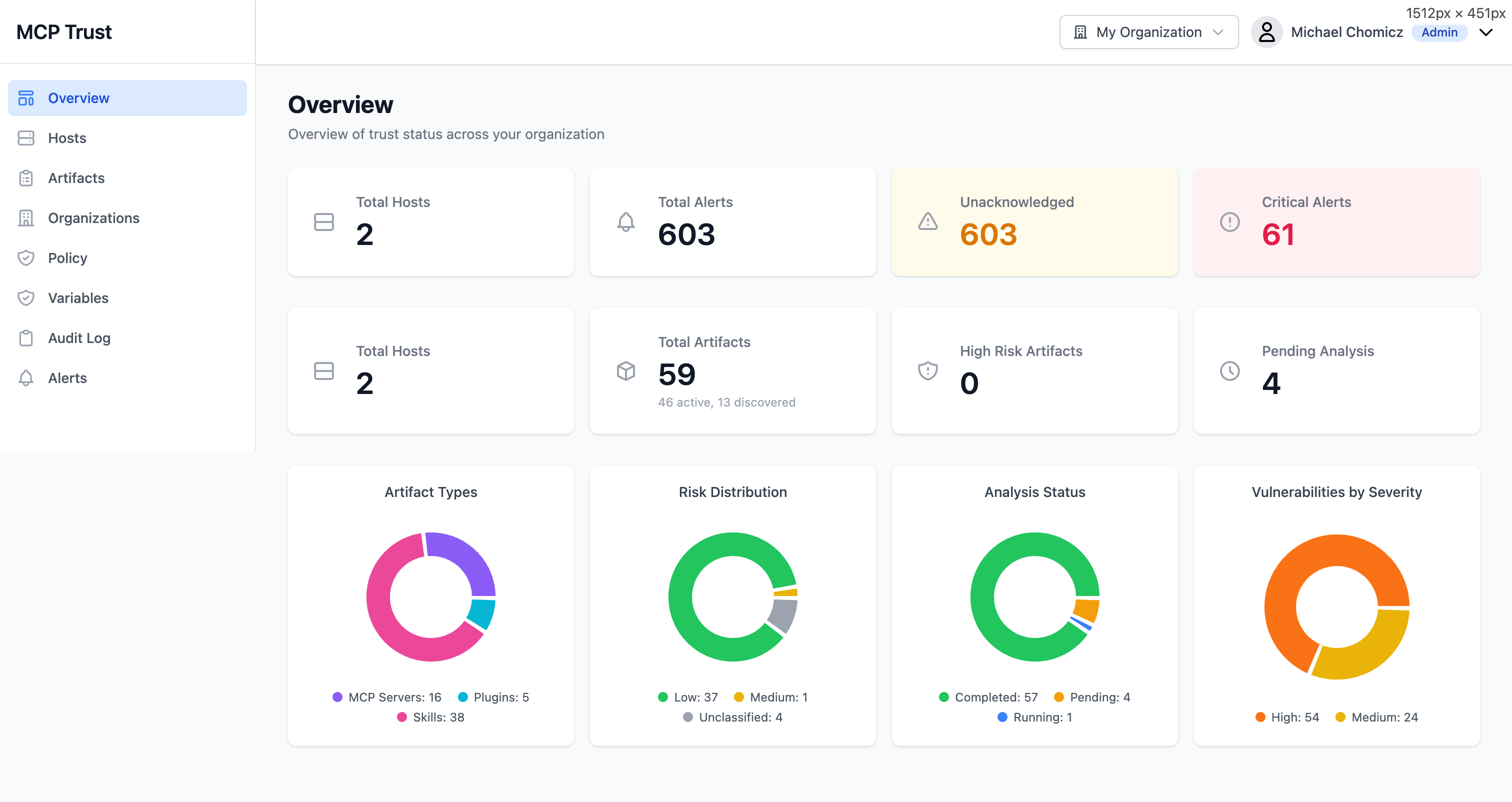
Continuous Monitoring
File watcher, periodic rescan, drift detection
|
Yesfsnotify + periodic rescan |
YesRuntime behavioral |
YesAgent observability |
YesSaaS activity |
YesRuntime inspection |
|
SIEM Integration
Signal files for endpoint security and SIEM platforms
|
YesMDE signal files, JSONL |
Unclear |
Unclear |
YesSentinel, CrowdStrike |
Unclear |
|
SARIF CI/CD Output
GitHub Code Scanning, GitLab SAST, Azure DevOps
|
Yesv2.1.0, --format sarif |
YesModel scanning only |
No |
No |
No |
|
Threat Framework Mapping
MITRE ATLAS, OWASP LLM, OWASP Agentic
|
YesAll three frameworks |
YesMITRE ATLAS |
YesOWASP, MITRE, NIST |
No |
YesOWASP, MITRE, NIST |
|
Remote Endpoint Trust Scoring
TLS, publisher, CVE tracking for MCP endpoints
|
YesAI research agent |
No |
PartialAllowlist/blocklist |
No |
PartialRisk scoring |
| OWASP LLM06:2025 Excessive Agency mitigation |
YesCommand + tool-call enforcement |
No |
No |
No |
PartialRuntime guardrails only |
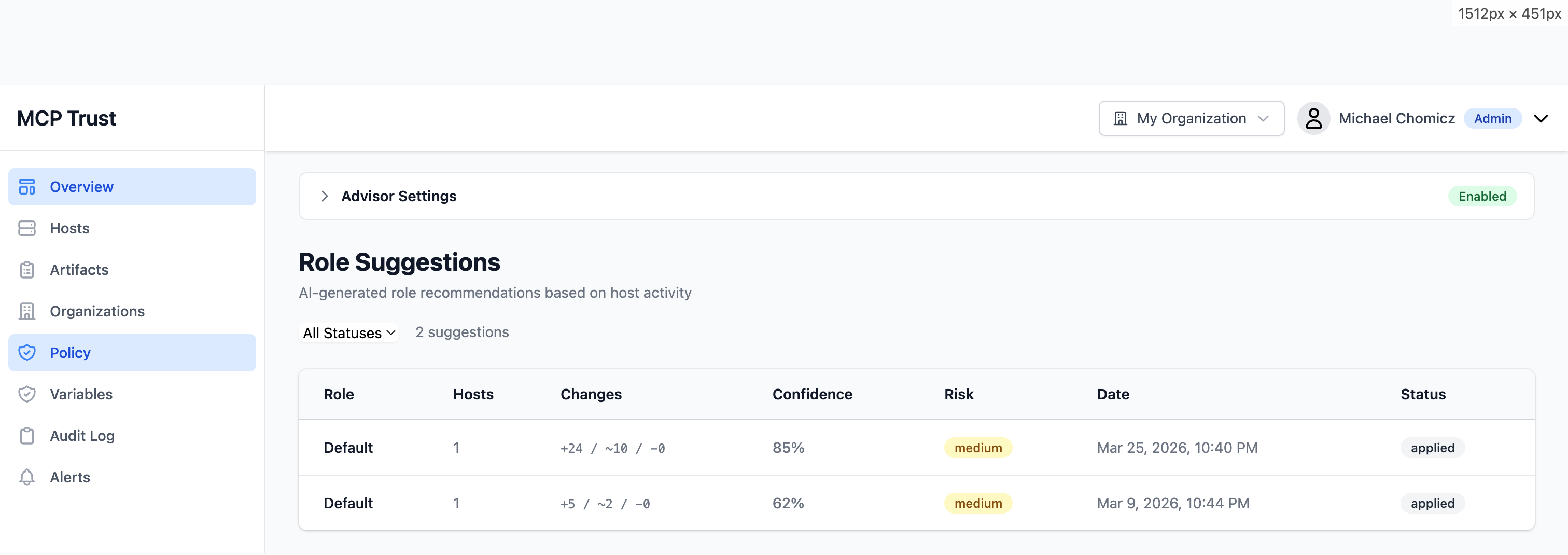
| AI-assisted policy recommendations |
YesPolicy Advisor with confidence scores |
No |
No |
No |
No |
| Deployment & Integration |
|
Single Binary CLI
curl | sh install, works without cloud dependency
|
YesGo binary, offline-capable |
NoEnterprise SaaS |
NoEnterprise SaaS |
NoEnterprise SaaS |
NoEnterprise SaaS |
|
Works Offline / Local-First
Scanning and enforcement without cloud connectivity
|
YesCloud enriches, not required |
No |
No |
No |
No |
|
Multi-Agent Support
Claude Code, Cursor, Copilot, any CLI-based agent
|
YesAgent-aware enforcement |
Partial |
YesSaaS + endpoint |
PartialSaaS agents only |
Yes |